The Ultimate Guide to Hiring a Hacker: Unveiling the World of Ethical Hacking Services
Within the shimmering, anonymous labyrinth of the digital era — where cybersecurity and privacy act as modern-day treasures that everyone craves — platforms such as Upwork have become relevant. These platforms offer valuable services to clients, including individuals and businesses. Particularly with the prevalence of various websites, devices, admin tools and Android digital platforms, security issues come to the fore. The idea of hiring a hacker, an image evoking shadowy figures feverishly tapping away at a limitless number of keyboard keys in darkened rooms, submerged in cascades of complex code and encrypted words, garners attention. However, as we unravel these mysteries, we discover white-hatted knights of the cyber realm — ethical hackers — whose services are intricately designed to protect, fortify and offer a solution to potential breaches.

When discussing hiring a hacker, we’re not endorsing any illicit cyber mischief. Instead, we’re illuminating the importance of legitimate, ethical hacking services — your secret weapon against potential digital threats. With a surge in cybercrime, it’s become paramount to safeguard our data, admin control, and clients’ information with the expertise of professional hackers. Platforms such as Upwork provide a number of professionals whose skills range from network security to Android system protection. Such services might cost money, but they ensure a sturdy firewall and a secure password system, providing peace of mind to any device owner, and adding an extra layer of design to your overall cybersecurity strategy.
In this comprehensive guide, we will navigate the ins and outs of utilizing ethical hacking services — a proactive step toward robust cybersecurity for both system admins and general users.
Understanding the Need for Hiring a Hacker
Ethical Hacking: What Is It? Ethical hacking is the authorized practice of bypassing system security to identify potential data breaches and threats in a network. The company that owns the system, along with its admin, consents to the hacking attempt to spot any vulnerabilities such as password weakness or firewall loopholes and get them rectified. Ethical hackers use their skills to improve security by cracking codes, decrypting words or guaranteeing tight Android security, so that systems are better defended against future attacks. These ethical hackers serve the clients by ensuring their digital privacy.
Common Scenarios for Ethical Hackers:
- Protecting sensitive personal data, such as on smartphones (hire a hacker for cell phone)
- Shielding businesses from cyber espionage (professional hackers for hire)
- Recovering access to social media and email accounts (hire a hacker to recover an account)
- Identifying and patching up security loopholes before they can be exploited
In these situations, ethical hackers act as paramount lines of defense for both system admins and clients. By simulating the strategies of malicious hackers, they offer a unique service that anticipates real threats and potential breaches, providing a crucial solution to potential cybersecurity issues.
Legal and Ethical Considerations: While the word ‘hacker’ typically carries a negative connotation, it’s essential to differentiate between the illegal activities carried out by black-hat hackers and the protective actions performed by ethical hackers. Hiring an ethical hacker should always invoke contracts that specify the scope of the work, ensuring all activities are legal, anonymous, and within the boundaries of consent.
Learn more about the ethics of hacking, and how it can serve to protect your devices, code, and money, giving peace of mind to system admins and their clients.
Let’s delve deeper into why one would hire a hacker, and how it could be the solution to admin’s and client’s cybersecurity worries.
Different Types of Hackers for Hire
When people consider hackers, they typically envision people who exploit technology for malicious gain. However, the hacking community is far more nuanced. Here, we categorize hackers based on their intentions and methods:

White Hat Hackers hacker for hire
These are the good guys — security professionals hired to find and fix vulnerabilities in systems. Hiring a white hat hacker involves a formal agreement in which they use their skills to fortify your cyber defenses, ensuring solid firewall protection and password security across your websites — helping to safeguard the digital privacy of both admins and clients.
Grey Hat Hackers hackers for sale
Operating in the murky space between legality and illegality, grey hat hackers may identify a security issue and report it to the organization. As experts in their field, they can be frequently found on platforms like Upwork, offering their services as knowledgeable programmers. They can sometimes ask for a small fee or recognition in return for their work. They generally do not have malicious intent, but their methods may not always be approved by the organization.
Black Hat Hackers
On the other side of the spectrum lie black hat hackers, who hack for personal gain, even breaching computer systems operated by even the most skilled programmers on different platforms like Linux and Windows. Their principal aim is often to spread malware, exploit vulnerabilities in social media platforms, or to steal, encrypt, or delete data, including digital currencies like bitcoin. These individuals and groups are the ones most often linked to cybercrime.
Choosing the right type of hacker, or information technology expert, for your demands is crucial. For legal and ethical considerations, always opt for a white hat hacker — their services are both legitimate and invaluable, serving as a reliable solution to protect your digital life. Remember, the intent behind the hack defines its nature. Ethical hacking services are not concentrated on harming but rather on improving, protecting, and preempting any possible breach. When you “hire hacker” services, you’re employing a digital bodyguard for your computer and social media platforms who can ward off Windows, Linux, and bitcoin-related threats. These expert programmers can deploy encryption software, bolstering your data security and making it less vulnerable to criminal activities.
By understanding the different types of hackers, or cybersecurity experts, you can make informed decisions about the services you require and who you choose to provide those services. An ethical hacker, for instance, might have a background in criminal investigation, enabling them to anticipate possible digital threats and prepare an appropriate response.
Discover the different hacker types and their motives as explained by experts in the field. Explore their unique features, areas of expertise like hacking on Windows, Linux platforms, cracking bitcoin wallets, and understand how protective measures like strong passwords can deter potential attacks even on social media platforms.
As you contemplate which type of hacker, or cybersecurity expert, best suits your needs, and which applications to defend like your computer and social media accounts, let’s turn our attention to the specific services they offer. This can range from encryption services to software penetration testing and more, provided by skilled programmers with knowledge of various systems.
Ethical hackers offer a wide array of services, each tailored to address specific vulnerabilities and concerns in personal and business networks. Engaging their expertise can be a game-changer in securing your digital assets, fending off criminal hacking attempts on Windows, Linux, and bitcoin wallets, and promoting software and data security.
Services Provided by Hackers
Penetration testing, or pen testing, is a simulated cyberattack where professional hackers, acting as expert programmers, look for exploitable vulnerabilities in your system — whether you’re on a computer, using social media platforms or handling bitcoin transactions. This comprehensive assessment provides insights into the system’s security posture.
Penetration Testing hacking service
For individuals who’ve lost access to their social media accounts, a hacker can help recover the account, ensuring you regain control and secure it against future attacks. If necessary, they, as experts in the field, can perform an investigation to identify the cybercriminals or culprits behind unauthorized account access, whether it be on a Windows, Linux or a bitcoin wallet.
- Network Services Test
- Web Application Test
- Wireless Network Test
- Social Engineering Test
Social Media Account Recovery hire a facebook hacker”, “hire an Instagram hacker
A security audit systematically evaluates the security of a company’s information system by measuring how well it conforms to a set of established criteria. This includes an app security analysis and audit to ensure your sensitive data is secure on all platforms. This audit encompasses verifying the effectiveness of the encryption tools and software safeguards in place, even down to how well they protect against attacks on social media platforms like Snapchat and bitcoin transactions.
Security Audits hacking services
Assessment simulations are controlled attacks that mimic phishing techniques to identify how employees retort, training them to recognize and report such attempts. Such drills can aid in assessing the potential for criminal infiltration in the system, be it on a Windows or Linux computer or within an app like Snapchat on social media platforms.
- Risk Assessment
- Vulnerability Scanning
- Security Polic Review
- Compliance Auditing
Phishing Simulations hire hackers
Hackers can also be hired for unique or unusual projects. They can assist with recovering lost passwords, delve into cyberbullying incidents on apps like Snapchat, identify the source of a targeted attack on windows or linux machines, or even help to secure bitcoin transactions or develop more secure communication methods for sensitive conversations on social media platforms. For instance, they might be skilled at creating custom encryption software for enhanced security, particularly if they’re proficient in protecting against Russian-origin malware or DDoS attacks which have recently gained notoriety.
Custom Requests and Situations hack hire
Ethical hackers can bring significant benefits in safeguarding your digital life. These members of the cybersecurity industry can offer unparalleled value by ensuring that your personal and professional digital assets are secure against the ever-growing threat of cyberattacks, even on apps like Snapchat.
Remember, research is crucial when opting for a hacking service, to ensure you’re dealing with a reputable professional. If the person you’re considering has involvement with respected organizations such as the International Council of E-Commerce Consultants, that’s a good sign. They offer a wealth of resources and certification programs for ethical hackers which adds credibility to their members.
Next up, let’s take a closer look at how you can find and vet these digital defenders. Remember, it’s not just about passwords and encryption, but also holistic security that includes a strong response mechanism to breach attempts and secure applications on platforms like Snapchat. A competent ethical hacker should be adept in countering everything from a Russian-originated DDoS attack to user credential theft.
As the need for robust cybersecurity measures becomes more pressing, finding the right ethical hacker for your specific needs is vital. Whether you need to guard against Russian-based cyber threats, keep track of the value of your digital assets, or protect your community members from phishing scams on apps like Snapchat, the ideal candidate will be able to handle it all.
How to Find a Qualified Hacker
The hunt for a proficient hacker begins with thorough research. You want someone reputable, like a person with a verifiable track record of protecting organizations from threats on platforms including Snapchat, as well as Russian cyber threats or DDoS attacks.
Researching and Vetting Potential Hackers (“how to find a hacker”, “hackers near me”)
Look for Certifications: Certifications carry great value, as reputable hackers often have credentials like the Certified Ethical Hacker (CEH) that verifies their skills.
- Check Online Community Forums: Online forums such as GitHub or Stack Overflow are fantastic resources for understanding an ethical hacker’s skills. Hackers who regularly contribute to discussions on preventing Russian-related malware or DDoS attacks or securing apps like Snapchat are likely to be of value.
- Explore Professional Networks: LinkedIn and other professional networking sites can be valuable resources for finding skilled ethical hackers who are proficient in protecting against cyberattacks on various platforms including Snapchat.Perhaps the person you’re seeking for has defended network members from Russian cyber threats in previous roles. One way to verify their skills would be through an analysis of their past performances in such scenarios.
- Ask for References: A capable hacker should provide references or case studies from users validating their skills against Russian or DDoS attacks. These can serve as significant evidence of their adeptness in handling cyber threats.
- Review Their Work: Reviewing a person’s content like blogs, white papers, or conference talks, and even their YouTube videos can give you an idea about their expertise piece by piece. What value do they bring to the cybersecurity community? How have they defended its members? There are numerous online platforms where companies and individual customers can connect with hackers for hire. Sites like HackenProof or CrowdSource offer a roster of vetted professionals to choose from, with many likely skilled in protecting products, securing WordPress sites, or safeguarding emails against potential hacks. Such platforms typically target an array of customers, from major businesses to the individual freelancer, and the detail of their work kind tends to hinge on the availability of specific skills or services.
- Check Service Offerings: Ensure the platform offers the specific service users require, be it penetration testing, social media account recovery, or securing products and WordPress sites, and protecting emails from hacks. With the right detail paid to these factors, customers of any kind can find the service that best targets their needs.
Using Online Platforms and Marketplaces online hacker
Read Reviews and Ratings: Past client feedback can offer valuable insights into a hacker’s reliability and quality of work. Client testimonials, for example, can provide real-world examples of a hacker’s success in securing products or emails or avert hacks. The freelancer market also relies heavily on reviews and ratings due to its inherent job-by-job work availability.
- Secure Communication: Platforms usually provide secure channels for users to discuss their requirements without compromising on confidentiality. This ensures safe navigation of discussions about protecting products, safeguarding WordPress sites, and securing emails against hacks. Secure communication is a crucial ingredient in any kind of professional partnership, but it becomes even more important when detailed and sensitive targets like client confidentiality are involved.
- A hacker’s skill level is often demonstrated through various certifications. The CEH, Offensive Security Certified Professional (OSCP), and CompTIA Security+ are industry-recognized certifications that can attest to a hacker’s expertise in managing and preventing hacks and protecting user credentials. These certifications highlight a freelancer’s or professional’s availability to handle projects of detail and scope.
- Find certified ethical hackers: This step is essential to make sure that the potential hacker has the expertise and can cater to the needs of specific customers. Their skills should encompass vital arenas like protecting products, securing WordPress sites, and safeguarding emails from probable hacks. Such detail will help you target the best freelancers for your project.
Checking Qualifications and Certifications
Detailed client testimonials can provide real-world examples of a hacker’s success. Look for detailed accounts that describe the nature of the project and its outcomes, especially those that involve securing products, protecting emails, and halting potential WordPress site hacks.
Armed with this knowledge, you’re ready to initiate the hiring process for a hacker who can serve your cybersecurity needs effectively, ensuring user credentials are protected, emails are safe, WordPress sites are secure, and products remain unhacked. Freelancers are often a valuable ingredient in this process due to their flexible availability and potential capacity for more detailed attention.
Reading Reviews and Testimonials “hacker-for-hire”
Once you have identified potential candidates, the next step is to understand the hiring process, highlighting your specific needs, such as preventing hacks, securing WordPress sites, protecting emails, and safeguarding products. This will help ensure clear expectations, a smooth collaboration, and successful outcomes for your security project, whether you’re a group of developers working on a new server, a business owner worried about Microsoft software vulnerabilities, or a freelancer seeking to enhance security levels.
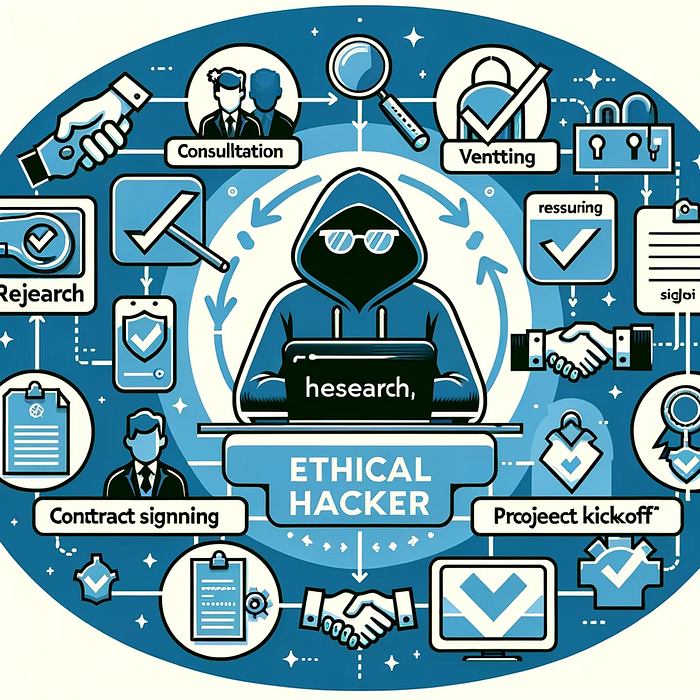
Start with an initial consultation to discuss your concerns and objectives. It may be different categories of data breaches you’re worried about, or securing specific jobs’ sensitive information. This conversation should help you clarify the scope of the project and if the hacker’s expertise aligns with your needs.
The Process of Hiring a Hacker
It’s crucial to set achievable goals and agree on deliverables. Detailed ambitions can help you target the most effective strategies for your company or project. Remember that every kind of interaction, from a detailed consultation to the agreement on deliverables, contributes to the overall health and success of your cybersecurity efforts.
Initial Consultation and Project Scope (Keyword: “hire a hacker online”)
It’s crucial to set achievable goals and agree on deliverables. This may include detailed reports, price-effective recommendations for security improvements, or confirmation of data recovery.
- Establish Goals: Be clear about what you hope to achieve with the hacker’s services.
- Scope of Work: Define the parameters and limitations of the project upfront.
- Confidentiality: Ensure a non-disclosure agreement (NDA) is in place to protect sensitive information.
Discussing the Goals and Deliverables
Pricing for hacking services can vary widely like server maintenance costs or Microsoft software licenses, so it’s important to understand the fee structure. Some hackers may charge hourly rates, while others may have flat fees for specific services.
- Timeline: Agree on a timeline for the deliverables.
- Milestones: Set benchmarks for progress, especially for longer engagements.
Understanding Pricing and Payment Terms, rent a hacker
Regular communication with the hacker is key to a successful engagement. For example, developers should keep a clear line of communication open about potential server weaknesses. Agree on the frequency and method of updates to keep the project on track.
- Discuss Costs: Be upfront about your budget and discuss costs early on.
- Payment Terms: Clarify payment terms, including any upfront deposits and payment schedules.
Establishing Communication and Progress Updates
By following these steps, you can confidently move forward to hire a hacker that meets your cybersecurity needs. The process should be transparent, professional, and secure, leading to a partnership that safeguards your digital assets against threats, be it a massive server or specific software.
- Regular Updates: Establish a schedule for progress updates.
- Points of Contact: Determine who will be your main point of contact for questions and updates.
Before finalizing the deal, let’s delve into a crucial aspect that can’t be overlooked — safety and legal considerations, especially when dealing with sensitive matters like server security or Microsoft software vulnerabilities.
In the realm of cybersecurity, whether for developers or other more typical jobs, hiring a hacker is a sensitive matter laced with ethical implications and legal constraints. Engaging a hacker’s services must be done with utmost caution to ensure that all activity is above board and in the best interest of data protection.
Safety and Legal Concerns
When seeking out a hacker, it is critical to verify that they adhere to ethical guidelines and operate within the legal framework of your jurisdiction, whether you’re concerned about a Microsoft software vulnerability or safeguarding your server. Here are a few steps to ensure a safe engagement:
Ensuring Ethical and Legal Services ( “ethical hacking”, “legal hacker services”)
To maintain the integrity of your data and protect your privacy in any situation- be it for developers or jobs dealing with customer’s data:
- Legal Compliance: Confirm that the hacker follows local and international laws regarding cyber security and data privacy.
- Ethical Standards: Choose a hacker who is committed to ethical standards as set by governing bodies like the International Council of E-Commerce Consultants).
- Written Agreements: Always formalize the engagement with a contract detailing every aspect of the project, including scope, confidentiality, and legal obligations.
Confidentiality Agreements (“professional hacker”)
The line between ethical hacking and cybercrime can be thin, and crossing it can have severe legal repercussions for those involved in server maintenance or Microsoft software development. Always:
- Non-disclosure Agreements (NDAs): Insist on signing NDAs to ensure that any information shared with the hacker remains confidential.
- Data Handling Protocols: Discuss and agree on how data will be handled, stored, and disposed of after the project concludes.
Staying within Legal Boundaries
Understand the legal aspects of hacking. It’s imperative to be aware and conscious about this to protect yourself and your systems. One of the ways you can achieve this is through diligent research on available resources such as Google, aiding your ability to keep your operations legal and ethical when considering things like server defense or Microsoft product security.
- Background Checks: Conduct thorough background checks to weed out individuals with questionable histories.
- Clear Boundaries: Set clear boundaries regarding the methods employed during the hacking process.
- Regular Audits: Consider regular audits to ensure continual compliance with all agreed-upon ethical and legal standards.
By taking these precautions, you can create a secure environment for hiring a hacker that champions transparency, trust, and above all, legal and ethical compliancy. This is true whether you’re a team of Microsoft developers or a small business owner.
With a comprehensive understanding of how to navigate the hiring process safely and legally, you can confidently move forward and begin interviewing candidates for the hacker job.
Ensuring a positive and fruitful partnership with a hacker involves clear communication, realistic expectations, and a methodical approach to tackling problems. Here are some recommendations to leverage your ability and make the most out of your engagement with a cybersecurity expert.
Tips for a Successful Engagement with a Hacker
Meticulous communication lays the foundation for any successful project, especially with data-sensitive jobs or server vulnerabilities. Articulate your concerns clearly and understand the proposed solutions:
Clear and Concise Communication (“i need a hacker to help me”)
Cybersecurity is a complex field, and not all problems have quick fixes, just like other aspects of technology like server maintenance or Microsoft software updates. Setting realistic expectations can help in managing the project timeline and anticipated outcomes:
- Regular Meetings: Schedule periodic meetings to discuss progress and any emerging concerns.
- Documentation: Request comprehensive documentation of findings and recommendations for your records.
Setting Realistic Expectations find a hacker
Cybersecurity is a complex field, and not all problems have quick fixes. Setting realistic expectations can help in managing the project timeline and anticipated outcomes:
- Outcome Clarity: Understand what is achievable and what is not, to avoid disappointment.
- Flexibility: Be prepared for some flexibility in the scope and duration of the work as challenges arise.
Dealing with Setbacks and Challenges
Anticipate that not all engagements will go smoothly; unforeseen challenges may crop up, and knowing how to handle them is key:
- Troubleshooting Protocol: Establish a protocol for addressing any problems or setbacks that may occur.
- Expert Advice: Consider expert opinions on the best course of action when challenges are encountered.
Conducting Post-Engagement Assessment
Once the services have been rendered, conducting an assessment can provide insights:
- Review the Impact: Evaluate the effectiveness of the hacker’s work in improving your cybersecurity posture.
- Feedback Loop: Provide feedback about the services received and any areas for improvement.
By adhering to these tips, you can assure a constructive and beneficial engagement that not only improves your cyber defenses but also empowers you with knowledge and best practices in cybersecurity.
In conclusion, hiring a hacker is a strategic decision that can fortify your defenses against the evolving landscape of digital threats. Keep these guidelines in mind, do your due diligence, use tools like Google to enhance your understanding, and you’ll be well on your way to establishing a secure digital presence.
Insert internal links here.
Are you ready for a deep dive into related services and future trends in the world of ethical hacking? Let’s take a look at what’s next for cybersecurity services.
Related Services and Considerations
Beyond the immediate need to hire a hacker for specific tasks, it’s important to consider a holistic approach to your cyber defense strategy. This includes ongoing cybersecurity support and being aware of supplementary measures you can take to bolster your digital security.
Ongoing Cybersecurity Support ( “hire phone hacker”, “online hackers”)
Ethical hackers can provide valuable ongoing support to ensure that your systems remain secure against new and evolving threats:
- Continuous Monitoring: Implementing round-the-clock surveillance to detect and respond to threats in real time.
- Regular Upgrades and Patches: Staying ahead of attackers by regularly updating and patching systems.
Supplementary Security Measures Following a Hack
After a hacker has assessed your system, it’s crucial to take their recommendations to heart:
- Implement Best Practices: Adopt recommended policies and procedures to mitigate future risks.
- Employee Training: Conduct regular cybersecurity training for your team to prevent social engineering and phishing attacks.
Future Trends in Ethical Hacking Services
The field of ethical hacking is constantly advancing. Staying informed about trends can help you anticipate the need for further services:
- Artificial Intelligence (AI) and Machine Learning (ML): Hackers are increasingly using AI and ML to predict and respond to cyberattacks.
- Internet of Things (IoT) Security: As everyday devices connect to the internet, securing them becomes a focus for ethical hackers.
By staying informed and engaged with cybersecurity trends and services, you can maintain a strong security posture that adapts to the changing threat landscape.
Insert internal links here.
In wrapping up, remember that cybersecurity is not a one-time fix but an ongoing process. Engaging with ethical hackers is a wise investment in your digital health. To safeguard your digital ecosystem against the endless sea of cyber threats, consider hiring a hacker as part of a comprehensive cybersecurity strategy. Browse Google for the latest cybersecurity trends and ways to enhance your digital defense. Stay vigilant and proactive to navigate the digital world safely and confidently.
FAQs Section:
- Q: What is the cost to “hire a hacker”?
- A: Costs can vary depending on the complexity of the task and the hacker’s skill level. It’s best to discuss your budget and requirements during the initial consultation.
- Q: How to ensure I “hire a hacker” discreetly?
- A: Only work with reputable professionals who are committed to confidentiality and sign NDAs to protect your privacy.
- Q: How long does it typically take to “hire a hacker” and see results?
- A: The timeframe can vary widely based on the scope of the project. Setting clear expectations and milestones can help manage the timeline effectively.
- Q: Is it possible to “hire a hacker” for one-time tasks?
- A: Yes, many ethical hackers offer services for specific one-time projects, from security audits to account recovery.
Remember to stay informed, prioritize transparency, and keep cybersecurity at the forefront of your digital strategy. A secure digital environment is the bedrock upon which the success of modern enterprises is built.